Benefits of Centralized and Standalone Access Control Systems
Written by:

Kostiantyn Oliynyk
Head of IoT at Webbylab
With a robust academic background in Telecommunication Systems Engineering, I apply my knowledge to lead innovations in the IoT domain. Starting as the first team member in the newly formed IoT department at WebbyLab, I've spearheaded its growth, fostering the expansion into embedded and hardware development alongside our core software projects. My dedication lies in pushing the boundaries of IoT technology, fostering a culture of innovation and excellence that profoundly impacts our clients' operational success.
FAQ
What is the difference of standalone and centralized access control systems?
As the name suggests, centralized ACSs involve centralized management of all locations. In contrast, standalone solutions work independently, allowing businesses to control access to each facility separately.
Which is safer: centralized or decentralized access control systems?
Both centralized and decentralized access control systems can be secure if implemented correctly. The level of security mostly depends on the measures that businesses apply: fingerprint or other biometric authentication methods, a door access card or other identifiers, the availability of alarm monitoring and video surveillance, etc.
Which type of access control system is better?
It’s impossible to state that any of these systems (centralized or standalone) is better. It depends on your business requirements, and both options are viable.
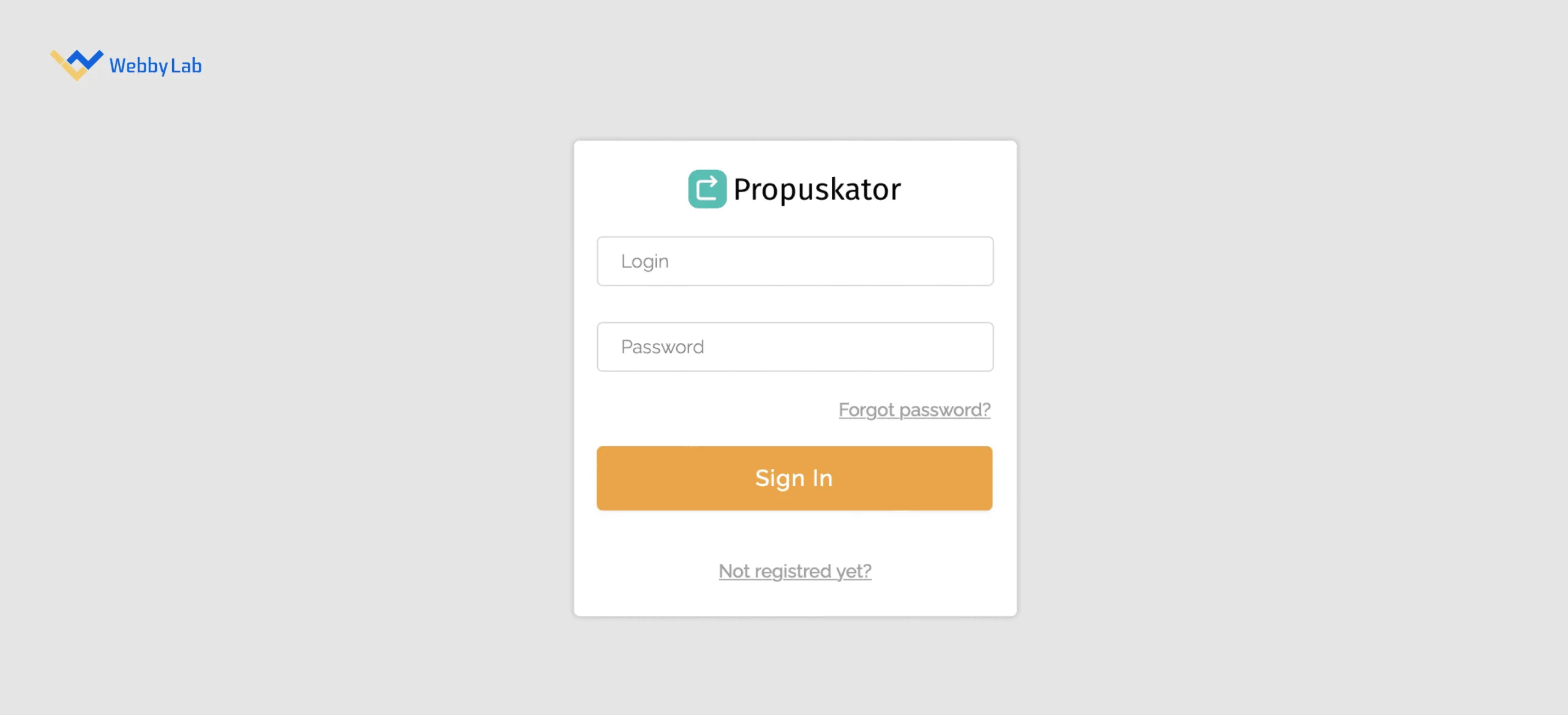
How can WebbyLab help with centralized and standalone access control system challenges?
WebbyLab can tackle any access control system challenges: guidance on the right ACS selection, deployment in different locations, integration with existing infrastructure, and more. We have a profound background owing to our Propuskator project and can leverage best practices to ensure the protection of your assets.